
Security in the network with Kali Linux
Watchful Dragon
One of the most demanding tasks for network administrators is securing the LAN against attacks. In this context, admins must remember that infrastructure and data are threatened not only by external attacks but also by internal flaws that can cause significant problems.
Linux offers an almost endless variety of tools for performing tests and simulated attacks to help protect a network. However, the installation and configuration of individual tools is often time-consuming and complicated. The Kali Linux distribution specializes in testing and security solutions to take this work off your hands: It provides preconfigured versions of all the necessary tools out the box.
Getting Started
Kali Linux is available for various architectures as an approximately 3GB image [1]. After burning and booting the Live medium, the GRUB boot manager shows you several startup options for various Live modes or direct installation on disk. Forensic mode is a special feature here; it tells the Debian derivative to mount any external storage medium as read-only, which rules out any manipulation of storage devices that need to be forensically investigated.
Kali Linux boots to an inconspicuous Gnome desktop (Figure 1) that reveals a comprehensive menu structure after clicking on the Applications button in the panel bar at top left. In addition to the usual menu groups, three distribution-specific subgroups can be found: Electronics, Hamradio, and Kali Linux. The Kali Linux subgroup contains various security tools for any conceivable application scenario, Electronics is devoted to the Arduino single-board computer, and Hamradio contains the Chirp tool for programming amateur radios.
The traditional menus appear very tidy and only contain the most important software in terms of applications for end users, such as office, image editing, and multimedia.
Kali Linux Menu
The central Kali Linux menu organizes its software inventory by application scenarios based on your practical approach. For example, programs that are used to obtain information about existing IT installations can be found in the Information Gathering subgroup. Here you will find network scanners, protocol analyzers, and software that provides general information about the DNS system and routing. For most categories, Kali integrates several applications into the submenus, which means some fairly deep menu structures are needed to cover virtually all test scenarios (Figure 2).

The Vulnerability Analysis submenu includes several groups for identifying vulnerabilities on the network. Different tools to test the hardware, especially in larger installations, of network vendor Cisco can be found here. Additionally, you'll find network scanners that analyze open ports and programs that sound out the security of databases.
You will find more important applications for collecting and evaluating data traffic and for special services such as VoIP in the Sniffing/Spoofing submenu, which also includes applications for logging web traffic. The Wireshark and Ettercap programs, as the best-known representatives for data sniffing and analysis, stand out here.
The Web Applications submenu specifically deals with detecting vulnerabilities in web services and servers. These tools are primarily suited for securing your own web server or the applications running on it.
Tests
Kali Linux provides a large number of special applications for testing the security of the LAN and WLAN. The distribution organizes the corresponding programs into four subgroups: Password Attacks, Wireless Attacks, Stress Testing, and Hardware Hacking.
Tools from the Password Attacks group reveal weak passwords, and tools from the Wireless Attacks group deal with a variety of wireless technologies. This includes vulnerabilities in legacy WLAN installations as well as technologies such as Bluetooth and RFID. The latter are often used as access control systems in companies.
The Stress Testing subgroup includes a number of applications that test the load behavior of the LAN or WLAN; VoIP solutions can also be integrated into your tests. They tell you if the attacker can compromise individual systems in the intranet or the DMZ through targeted data flooding.
Kali Linux also explicitly includes network hardware in its corresponding test routines: Several tools thus test different manufacturers' routers for vulnerabilities.
Tools from the Hardware Hacking group carefully examine devices that run the Android operating system, including the Arduino single-board computer (SBC). Although SBCs are still not particularly widespread in the corporate IT environment, omnipresent mobile devices running Android, such as tablets and smartphones, represent a significant security risk if people integrate them into the local IT infrastructure without taking precautions. It is therefore advisable to check the configuration of these devices.
The applications listed in the Exploitation Tools subgroup are all about checking device-specific firmware – and services and operating systems – for known vulnerabilities. Negligence in terms of firmware updates or service configurations is quickly and reliably revealed. The Metasploit framework is the best known representative of this application group; it can perform attacks and tests against distributed infrastructures.
Several tools that can be used to install backdoors can be found in the Maintaining Access subgroup; this practice guarantees longer-term checking of access to external systems. Kali Linux distinguishes between operating system-specific backdoors and those for your web server.
Additional Software
As well as the actual security tests, increasing importance is attached to documenting standards and data reconstruction. In the Forensics group, Kali Linux provides applications that are used for forensic examinations of data storage devices and systems. These include, among other things, rootkit scanners and the Sleuth Kit software suite, which incorporates a variety of forensic tools. Additionally, Kali Linux offers a few programs for data reconstruction in this group; these tools can retrieve partitions and data on supposedly deleted storage media.
Very large and potentially confusing logging data sets naturally accumulate – particularly during penetration tests and while sniffing data traffic. To simplify analyzing this data, the developers of Kali Linux bundled an impressive number of documentation tools in the Reporting Tools submenu. These tools are not only used for writing reports, but they also provide support with comprehensive audit documentation. Additionally, programs can be found here that you can use to customize screencasts and screenshots of web pages from the command line.
Installation
Unlike standard distributions, Kali Linux also comes with special features for various installation options. The downloaded ISO image works relatively slowly on an optical disk; Kali runs much more smoothly from a bootable USB memory device. It can also be operated in a persistent mode, which makes permanent storage of configuration data possible.
However, a few additional steps are necessary to create the operating system in persistent mode on a USB stick. The USB stick itself should, in this case, have a capacity of at least 8GB, because you need to create a separate partition manually for storing the persistent data. On the other hand, a capacity of 4GB is enough for conventional Live use of the operating system. You will find detailed information about the different installation options on flash drives on the official documentation website [2].
Before creating a bootable medium, it is important to look at the system requirements: In the 32-bit version, Kali Linux uses a kernel with PAE extensions. Some older Intel processors from the Pentium M generation and many Atom processors do not support this extension. This means that Kali Linux cannot be installed or run on these systems.
If your network includes wireless components, or if you run it completely as a WLAN, you need to pay attention to the wireless network card in your computer. Some manufacturers do not provide any modules for Linux, and others only implement a limited set of features, meaning that some Kali Linux programs cannot be used with your WLAN hardware. WLAN chipsets from Atheros, Ralink, and Realtek generally work well with Kali. Thanks to the proprietary firmware integrated in the operating system, you can access WLAN chipsets from Intel in almost all cases. With older WLAN components from this provenance, however, switching to the monitor mode often does not work, so these components are of very limited use for analysis purposes.
When installing Kali Linux in persistent mode on a USB stick, additional drivers or updates are difficult to install. Therefore, it's advisable to install the system permanently on a dedicated computer, especially for administrators who want to use Kali Linux in large, heterogeneous environments. The advantage of this method is that system updates are performed without any problems. Furthermore, driver problems, which can occur when you use WLAN components, can be avoided with a fixed installation on a desktop or notebook PC. If, on the other hand, you use a USB stick on various computer systems with different hardware, you run a high probability of the system occasionally not detecting the hardware – as is the case with some WLAN chipsets – and not being able to switch to monitor mode.
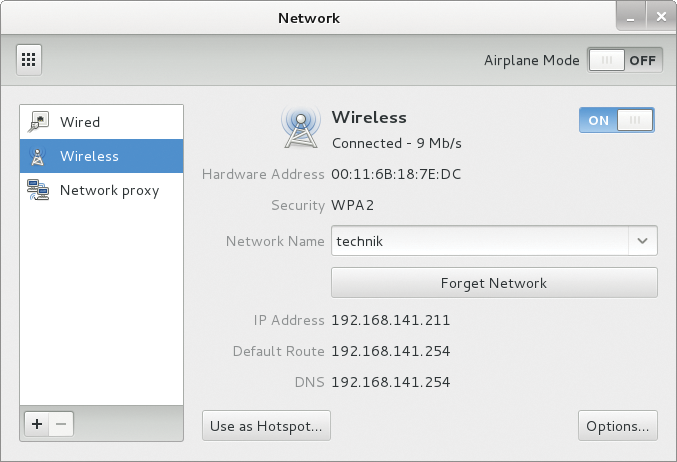
You can launch a permanent, fixed installation on a storage device in the GRUB boot menu by selecting the Install or Graphical install options. Kali Linux then starts the Debian installer, which will guide you through putting a working system on your hard disk in just a few steps. Because the installer wants to configure the network device – but needs a wired interface for this – you need to skip this step if you are only using a WLAN. After successfully installing the operating system on your disk and then rebooting, you can set up the WLAN configuration by selecting Applications | System Tools | Settings. In the dialog that opens, enter your WLAN credentials and add the Kali Linux system to your network (Figure 3).
Encryption
When installing the operating system on a USB stick or local mass storage, as well as the default settings, you also have the option to encrypt the disk. An encrypted disk ensures that, in the case of theft of the laptop or the USB stick with Kali Linux, the existing databases will not end up in the wrong hands.
The installation routine also offers the Guided – use entire disk and set up encrypted LVM option for partitioning your storage device. After you select this option, the installer creates an encrypted root partition and a swap partition on the device, unless you explicitly specify otherwise. If you want a different partitioning scheme, you can create this by selecting the appropriate options with encryption.
Conclusions
Kali Linux can be used universally both as a Live system from different boot media and as a static installation. The limitations associated with Live operation, however, make it advisable to install the operating system on dedicated mass storage. This setup rules out problems that typically occur from unsupported hardware in Live use on different computer systems. Additionally, Kali Linux can be kept constantly up to date with a static installation.
The system's software configuration appears to be well thought out in all modes and covers almost all conceivable operational scenarios. Kali Linux should therefore be a part of every serious administrator's basic technical configuration. In a future article, I will show you how to use the provided toolbox to detect vulnerabilities on your network quickly and reliably.
